Towards a First Step to Understand the Cryptocurrency Stealing Attack on Ethereum
Zhen Cheng, Xinrui Hou, Runhuai Li, Yajin Zhou, Xiapu Luo, Jinku Li, Kui RenProceedings of the 22nd International Symposium on Research in Attacks, Intrusions and Defenses (RAID 2019)
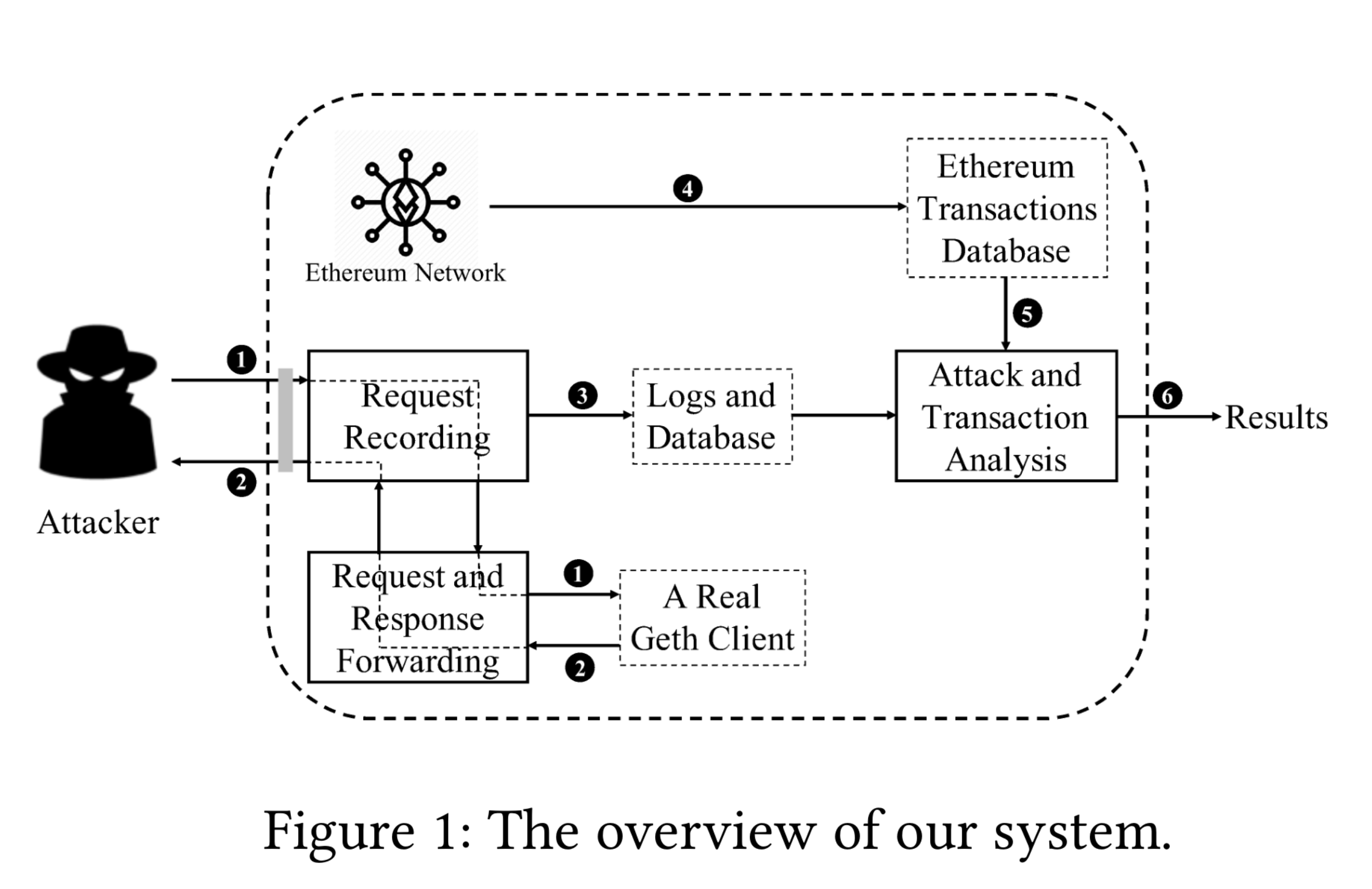
We performed the first systematic study of a new attack on Ethereum that steals cryptocurrencies. The attack is due to the unprotected JSON-RPC endpoints existed in Ethereum nodes that could be exploited by attackers to transfer the Ether and ERC20 tokens to attackers-controlled accounts. This study aims to shed light on the attack, including malicious behaviors and profits of attackers. Specifically, we first designed and implemented a honeypot that could capture real attacks in the wild. We then deployed the honeypot and reported results of the collected data in a period of six months. In total, our system captured more than 308 million requests from 1,072 distinct IP addresses. We further grouped attackers into 36 groups with 59 distinct Ethereum accounts. Among them, attackers of 34 groups were stealing the Ether, while other 2 groups were targeting ERC20 tokens. The further behavior analysis showed that attackers were following a three-steps pattern to steal the Ether. Moreover, we observed an interesting type of transaction called zero gas transaction, which has been leveraged by attackers to steal ERC20 tokens. At last, we estimated the overall profits of attackers. To engage the whole community, the dataset of captured attacks is released on https://github.com/zjuicsr/eth-honey.
@inproceedings{eth-honey,
author = {Zhen Cheng and Xinrui Hou and Runhuai Li and Yajin Zhou and Xiapu Luo and Jinku Li and Kui Ren},
title = {Towards a First Step to Understand the Cryptocurrency Stealing Attack on Ethereum},
booktitle = {Proceedings of the 22nd International Symposium on Research in Attacks, Intrusions and Defenses},
year = {2019},
}